Security Groups
- Admin-> Security Groups
-
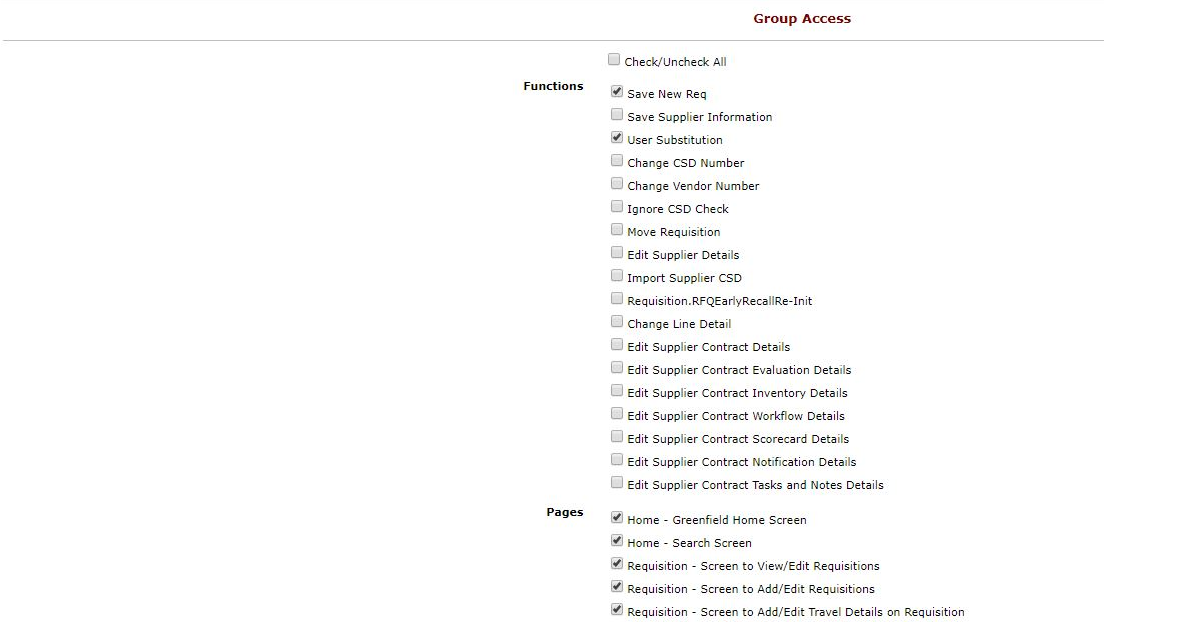
Security access is controlled via security groups. Each security group is granted certain accesses.
Users are then in turn assigned to one or more security group
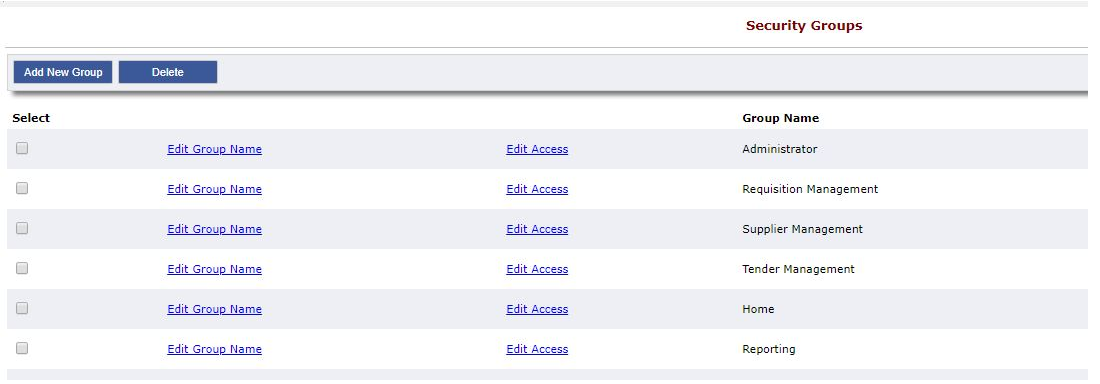
Users can be assigned any number of groups. Each user will inherit the permissions as set in the security group. Multiple security groups can have the same feature access.
- Date Created
- 2020/04/20 18:14:37
- ID
- 52